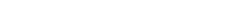
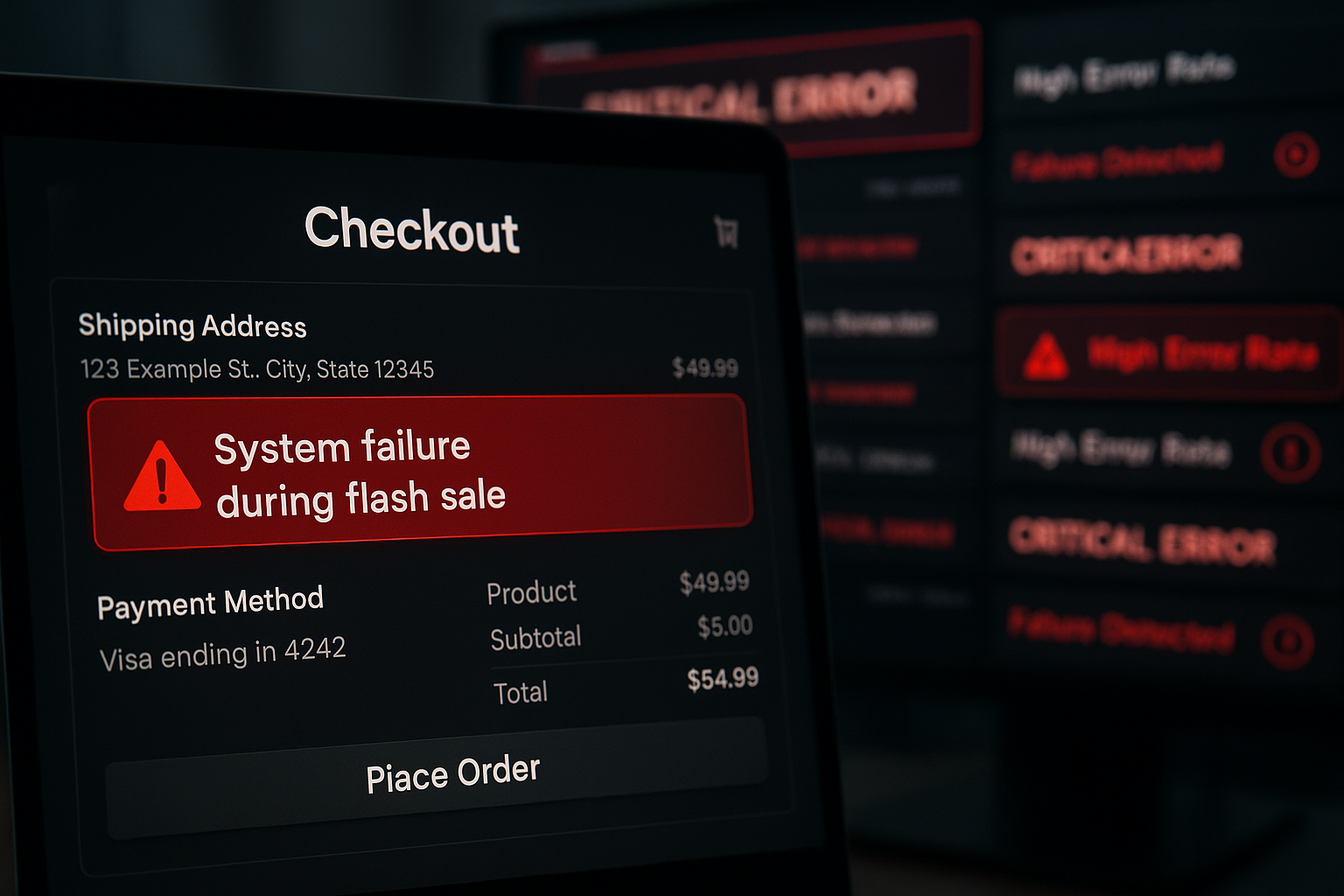
Picture this: a retail platform’s checkout system collapses 47 minutes into a flash sale. Monitoring dashboards turn red, the on-call SRE scrambles to scale infrastructure that should have been validated weeks ago, and revenue bleeds at roughly $12,000 per minute. Post-mortem cause? No one ran a load test against the new payment-gateway integration. The scenario is neither exotic nor rare – a NIST-commissioned study found that inadequate software testing infrastructure costs the U.S. economy between $22.2 billion and $59.5 billion annually, with more than half of that burden falling on end users forced into error-avoidance workarounds [1].
If you’re a QA lead, performance engineer, or engineering manager responsible for shipping reliable software at speed, you already know that “testing before release” stopped being sufficient years ago. What’s harder to navigate is the explosion of tooling categories – open-source utilities, SaaS-based platforms, enterprise-grade solutions – all claiming AI superpowers, all demanding evaluation time your team doesn’t have.
This guide isn’t another glossary entry or top-10 listicle. It’s a structured playbook that connects the why behind each QA decision to measurable outcomes: which testing types close the coverage gaps your team is likely carrying, how to build an automation strategy that doesn’t collapse under its own maintenance weight, how to evaluate tools without drowning in vendor noise, and where AI actually delivers production-ready value today. Think of it as the resource a senior QA lead would hand you on day one – five pillars, zero filler.
- What Is QA Testing? (And Why ‘Just Testing Before Release’ Isn’t Enough Anymore)
- The Complete QA Testing Types Taxonomy: What to Test, When, and Why
- Test Automation in 2026: From Framework Setup to AI-Powered Intelligence
- Step 1: Choosing the Right Test Cases to Automate (The Automation Pyramid in Practice)
- Setting Up Your Automation Framework: Architecture Decisions That Prevent Technical Debt
- AI-Powered Test Automation: Self-Healing Scripts, Intelligent Correlation, and What’s Actually Production-Ready Today
- No-Code and Low-Code Test Automation: Expanding QA Beyond the Scripting Team
- How to Choose QA Testing Tools Without Getting Lost in the Vendor Noise
- Building a QA Strategy That Scales: From Reactive Firefighting to Proactive Quality
- Frequently Asked Questions
- References and Authoritative Sources
What Is QA Testing? (And Why ‘Just Testing Before Release’ Isn’t Enough Anymore)
QA testing is a process-oriented discipline aimed at preventing defects through systematic activities embedded across the entire software development lifecycle – from requirements analysis through post-deployment monitoring. It is not synonymous with running test cases before a release date. The ISTQB® Certified Tester Foundation Level (CTFL 4.0) syllabus, the internationally recognized professional standard for software testing, defines quality assurance as a set of activities focused on providing confidence that quality requirements will be fulfilled [2]. That distinction matters: QA builds quality into the process; testing measures the product.
The quality analyst role has evolved accordingly. A modern quality analyst writes risk-based test plans, defines acceptance criteria collaboratively with product and engineering, maintains regression suites, designs automation strategies, monitors production telemetry for quality signals, and increasingly evaluates AI-assisted testing tooling. The ISTQB now offers dedicated certifications in Test Automation Strategy (CT-TAS) and AI Testing (CT-AI), reflecting that automation architecture and machine-learning literacy are now formal competencies expected of QA professionals [2].
QA vs. QC vs. Testing: Understanding the Distinctions That Matter
Teams frequently use QA, QC, and Testing interchangeably. This creates scope confusion and misaligned ownership. Here’s the ISTQB-grounded distinction:
| Dimension | Quality Assurance (QA) | Quality Control (QC) | Testing |
|---|---|---|---|
| Focus | Process improvement | Product inspection | Execution & defect detection |
| Activity Type | Proactive (prevent defects) | Reactive (find defects) | Specific execution within QC |
| When Applied | Throughout the SDLC | After development stages | During specific test phases |
| Who Owns It | QA lead / process team | QA engineers / testers | Test engineers / automation |
| Example | Defining code-review standards | Reviewing test results against pass/fail criteria | Running a regression suite against a staging build |
Getting this taxonomy right determines whether your team treats QA as a phase (reactive, expensive) or a practice (proactive, cost-effective).
The Role of a Quality Analyst: From Bug-Finder to Quality Architect
The 90,500 monthly searches for “quality analyst” reflect genuine career and organizational interest in this role – but most search results deliver thin job-description summaries. Here’s what the role actually demands in 2026:
Core competencies of a modern quality analyst:
- Risk-based test planning – prioritizing test coverage by business impact, not just code coverage percentage
- Automation scripting and framework maintenance – writing, reviewing, and refactoring test scripts across UI, API, and integration layers
- Performance testing awareness – understanding load profiles, SLA thresholds (p95 latency, error rates, Apdex), and when to escalate to dedicated performance tooling based on the performance metrics that matter in performance engineering
- CI/CD pipeline integration – configuring test triggers, quality gates, and automated reporting within deployment pipelines
- Defect lifecycle management – triaging, reproducing, and classifying defects with sufficient diagnostic data for developers
- AI/ML testing literacy – evaluating AI-assisted tools, understanding self-healing locator behavior, and reviewing AI-generated test cases for coverage accuracy
- Cross-functional collaboration – translating business requirements into testable acceptance criteria with product managers, and reviewing implementation approaches with developers before code is written
Why QA Pays for Itself: The Cost of Defects at Every Development Stage
The financial case for QA investment is not theoretical. The NIST Planning Report 02-3 compiled data (drawing on Boehm 1976 and Baziuk 1995 studies) showing that defects discovered post-release cost up to 880 times more to repair than defects identified at the requirements stage [1]. That multiplier reflects the cascading cost of rework: redesign, re-implementation, re-testing, hotfix deployment, customer communication, and reputation recovery.
DORA’s research reinforces this from the DevOps perspective: “Manual regression testing is time-consuming to execute and expensive to perform, which makes it a bottleneck in the process. Software can’t be released frequently and developers can’t get quick feedback” [3]. Teams stuck in manual-regression bottlenecks don’t just ship slower – they accumulate unvalidated risk with every delayed release cycle.
The Complete QA Testing Types Taxonomy: What to Test, When, and Why
No single testing type provides adequate coverage alone. A coherent QA strategy layers multiple testing types according to when defects are cheapest to detect and which system properties each type validates. The ISTQB CTFL 4.0 classification divides testing into functional (does it do what it should?) and non-functional (how well does it do it?) – a distinction that determines tooling requirements, team skills, and CI/CD pipeline design.
Functional Testing: Verifying That Your Software Does What It’s Supposed To
Functional testing validates behavior against specified requirements. These types form the foundation of DORA’s test automation pyramid [3]:
| Testing Type | What It Validates | Automation Suitability | CI/CD Pipeline Stage |
|---|---|---|---|
| Unit | Individual functions/methods in isolation | High | Every commit |
| Integration | Interactions between modules, services, or APIs | High | Every merge to main |
| Smoke | Core critical paths after a new build | High | Post-build, pre-deploy |
| Regression | Previously working functionality after code changes | High | Pre-merge, nightly |
| System | End-to-end workflows in a production-like environment | Medium | Pre-release |
| Acceptance (UAT) | Business requirements satisfaction | Medium-Low | Pre-release gate |
| Sanity | Narrow targeted verification after a specific fix | Low (usually manual) | Ad-hoc |
The pyramid principle is straightforward: unit and integration tests should vastly outnumber end-to-end tests. A team with 2,000 unit tests, 300 integration tests, and 50 UI tests will get faster, more reliable feedback than one with 50 unit tests and 500 brittle end-to-end scenarios.
Non-Functional Testing: The Performance, Security, and Reliability Layer Teams Often Skip
Non-functional testing validates system qualities – speed, capacity, resilience, security – that users experience but requirements documents often underspecify. The NIST Planning Report explicitly classifies performance testing as a specialized testing stage, noting: “A major benefit of performance testing is that it is typically designed specifically for pushing the envelope on system limits over a long period of time. This form of testing has commonly been used to uncover unique failures not discovered during conformance or interoperability tests” [1].
The ISTQB’s dedicated CT-PT (Performance Testing) certification validates that this category demands its own methodology and tooling – not ad-hoc script modifications from your functional test suite [2].
Key non-functional testing types:
- Performance testing – validates response times under expected load (target: p95 response time < 500ms for critical API endpoints)
- Load testing – measures system behavior under anticipated concurrent user volumes (e.g., 10,000 simultaneous sessions); for a deeper walkthrough, see this beginner’s guide to load testing
- Stress testing – pushes beyond expected load to identify breaking points and failure modes
- Scalability testing – validates that adding infrastructure (horizontal or vertical) produces proportional throughput gains
- Security testing – identifies vulnerabilities through penetration testing, static analysis, and dependency scanning
- Compatibility testing – verifies behavior across browsers, OS versions, and device configurations
Teams that skip non-functional testing are essentially deploying to production and hoping their monitoring catches problems before customers do. That’s not a QA strategy – it’s incident-driven development.
Manual vs. Automated Testing: A Practical Decision Guide (Not a Binary Choice)
Automation isn’t a goal; it’s a tool. The right question isn’t “should we automate?” but “which tests deliver the highest ROI when automated, and which benefit from human judgment?”
Automation candidacy decision matrix:
| Test Scenario | Automation ROI | Rationale |
|---|---|---|
| Login/authentication regression | High | Runs daily, deterministic inputs, fast, clear pass/fail |
| API contract validation | High | High frequency, schema-checkable, CI/CD gateable |
| Cross-browser visual regression | High | Tedious manually, pixel-diff tools mature |
| First-time user onboarding UX evaluation | Low | Requires human judgment on flow intuitiveness |
| Exploratory edge-case discovery | Low | Non-deterministic, depends on tester creativity |
| Performance baseline validation under load | High | Requires automated orchestration of concurrent virtual users |
| Accessibility compliance (WCAG audit) | Medium | Automated scanning catches ~30-40% of issues; human review required for contextual violations. |
DORA’s research confirms the direction: teams where “developers are primarily responsible for creating and maintaining suites of automated tests” show measurably improved software delivery performance [3].
Test Automation in 2026: From Framework Setup to AI-Powered Intelligence
AI test automation tools have surged 234.72% in search interest, and no-code test automation adoption has grown 29.11% – reflecting a market that’s moved well past the “should we automate?” question into “how do we automate intelligently?” DORA’s causal research is unambiguous: “DORA’s research shows that continuous automated testing also drives improved software stability, reduced team burnout, and lower deployment pain” [3].
The ISTQB now offers CTAL-TAE v2.0 (Test Automation Engineering) covering “the design, development, and maintenance of test automation solutions” and CT-GenAI for “testing with Generative AI techniques across the entire test process – from requirements analysis and test design to automation, reporting, and continuous improvement” [2].
Step 1: Choosing the Right Test Cases to Automate (The Automation Pyramid in Practice)
Before selecting any framework, score each test case against automation-readiness criteria:
| Criterion | Score 1 (Low) | Score 2 (Medium) | Score 3 (High) |
|---|---|---|---|
| Run Frequency | Monthly or less | Weekly | Daily or per-commit |
| Input Determinism | Variable/exploratory | Semi-structured | Fully deterministic |
| Execution Time (manual) | < 2 minutes | 2 – 15 minutes | > 15 minutes |
| Failure Signal Clarity | Ambiguous / subjective | Partially automatable assertion | Clear pass/fail criteria |
Score ≥ 10: Automate immediately. Score 7–9: Strong candidate, schedule for next sprint. Score ≤ 6: Keep manual or revisit after stabilization.
Example: Login regression test – run frequency: daily (3), deterministic: yes (3), manual execution: 5 minutes (2), clear pass/fail: yes (3). Total: 11 → automate first.
QA Engineer’s Perspective: One of the most common automation mistakes is teams automating the wrong tests first – high-variability exploratory scenarios instead of the deterministic regression suite that runs 50 times a day. Get the pyramid right before chasing AI features.
Setting Up Your Automation Framework: Architecture Decisions That Prevent Technical Debt
The ISTQB CTAL-TAE v2.0 framework defines automation architecture as encompassing test design, execution, reporting, and maintenance integration with configuration management [2]. Here’s a practical setup checklist:
- Define automation scope and pyramid layer – map each automated test to its pyramid tier (unit/integration/UI)
- Choose test runner and reporting format – standardize on a runner that outputs CI/CD-parseable results (JUnit XML, Allure)
- Apply design patterns – the Page Object Model (POM) separates UI element locators from test logic. Teams using POM report 40–60% fewer script failures after UI redesigns because locator changes propagate from a single source file, not across hundreds of test methods
- Configure CI/CD trigger hooks – unit tests on every commit, integration tests on merge, full regression nightly; for guidance on embedding performance validation into these pipelines, see integrating performance testing in CI/CD pipelines
- Establish script maintenance rotation – assign ownership of automation suite health as explicitly as you assign on-call rotations; unowned suites decay within weeks
AI-Powered Test Automation: Self-Healing Scripts, Intelligent Correlation, and What’s Actually Production-Ready Today
The AI testing landscape splits into production-ready capabilities and emerging ones. Here’s an honest assessment:
Production-ready today:
- Self-healing locators – when a UI element’s ID or class changes, AI identifies the most probable replacement using surrounding DOM context. Reduces nightly test suite failures by 20–40% in teams with frequent UI updates.
- Intelligent correlation – WebLOAD by RadView’s AI-accelerated correlation engine automatically identifies dynamic parameters (session tokens, CSRF values, server-generated IDs) that would otherwise cause script failures under load, dramatically reducing the manual correlation effort that traditionally makes load test scripting a multi-day bottleneck.
- AI-generated test data – synthetic data generation for parameterized tests, including edge-case values that human testers rarely construct manually.
Emerging (human review still essential):
- AI-generated test cases from requirements – LLMs can draft test scenarios from user stories, but coverage accuracy requires human validation. ISTQB’s CT-GenAI certification explicitly structures this as a human-supervised workflow [2].
- Autonomous exploratory testing – AI agents that navigate applications and flag anomalies show promise but produce high false-positive rates in complex, multi-step workflows.
- Predictive defect analysis – ML models trained on historical defect data can flag high-risk code changes, but require 12+ months of labeled defect data to achieve actionable precision.
No-Code and Low-Code Test Automation: Expanding QA Beyond the Scripting Team
No-code tools have grown 29.11% in adoption because they solve a real problem: QA analysts and business stakeholders who understand test scenarios deeply but can’t write automation scripts. These platforms use record-and-replay, visual flow builders, and natural-language test definitions to lower the barrier.
Where no-code works well: A product manager needs to validate that a new checkout flow works across three browsers before a release. A visual test builder captures the flow in 15 minutes, runs across browser configurations, and reports results – no scripting required.
Where no-code falls short: A microservices application requires authentication flows with dynamic OAuth tokens, multi-step API orchestration, and database state validation between steps. No-code tools struggle with custom token-handling logic, conditional branching based on API response payloads, and teardown scripts that reset test environments. At scale (500+ tests), maintenance overhead in visual editors often exceeds equivalent coded frameworks.
Trade-off summary:
| Factor | No-Code Benefit | No-Code Limitation |
|---|---|---|
| Onboarding speed | Hours, not weeks | – |
| Accessibility | Non-developers can author tests | – |
| Complex auth flows | – | Requires custom scripting workarounds |
| Scale (500+ tests) | – | Visual editor maintenance overhead |
| Performance/load testing | – | Not supported; requires dedicated tools |
| Vendor lock-in risk | – | Proprietary test formats, limited export |
How to Choose QA Testing Tools Without Getting Lost in the Vendor Noise
Every competitor article in this space jumps straight to a tool list. That’s backwards. Tool selection should begin with requirements definition, not vendor demos. The ISTQB CT-TAS (Test Automation Strategy) certification framework structures tool evaluation around team competency, automation scope, and integration requirements [2] – and that’s the approach we’ll follow here.
Step 1: Define Your Requirements Before You Open a Single Vendor Page
Requirements checklist (assess before evaluating any tool):
- Team scripting skill level – Can your team write and maintain code-based test scripts, or do you need no-code/low-code options?
- Application architecture – Web app, REST/GraphQL APIs, microservices, mobile, or a hybrid?
- Primary testing types required – Functional only, or functional + performance + security?
- CI/CD stack – What pipeline tools are you running (Jenkins, GitLab CI, GitHub Actions, Azure DevOps)?
- Deployment model – Cloud-only, on-premises, or hybrid? (This eliminates some SaaS-only platforms immediately.)
- Compliance requirements – SOC 2, HIPAA, PCI-DSS? Some tools lack on-prem deployment or audit-trail capabilities.
- Budget model – Per-user licensing, per-virtual-user, consumption-based, or open-source with internal engineering cost?
Team Profile Quick Assessment:
- If your team has 2+ engineers comfortable with JavaScript/Python AND you need performance testing: → Evaluate enterprise-grade solutions with scripting flexibility.
- If your team is primarily manual QA analysts AND you need functional UI testing: → Start with no-code/low-code SaaS platforms for functional coverage.
- If you have a mature DevOps practice AND need full-stack coverage (functional + performance + security): → Evaluate enterprise solutions with CI/CD-native integration and multi-protocol support.
QA Tool Categories Compared: Open-Source Utilities, SaaS Platforms, and Enterprise Solutions
Present an honest, balanced comparison of the three primary tool categories with transparent trade-off analysis. Open-source utilities offer flexibility and zero licensing cost but demand engineering investment and self-managed infrastructure. SaaS-based platforms provide fast onboarding and managed infrastructure but can create vendor dependency and may have coverage limitations for complex scenarios. Enterprise-grade solutions offer depth, support, and integration at scale but require investment justification. Avoid naming specific competitor tools – use category-level analysis.
| Evaluation Criterion | Open-Source Utilities | SaaS-Based Platforms | Enterprise-Grade Solutions |
|---|---|---|---|
| Licensing Cost | Free (but engineering time isn’t) | Subscription-based, scales with usage | Annual license, often volume-based |
| Onboarding Speed | Weeks (setup, configuration, infra) | Hours to days (managed infrastructure) | Days to weeks (with vendor support) |
| Automation Depth | High (full code control) | Medium (visual + limited scripting) | High (code + AI-assisted) |
| AI Integration | Community plugins, variable quality | Built-in for some platforms | Production-grade (e.g., AI correlation, anomaly detection) |
| Performance/Load Testing | Basic (limited concurrency, DIY infrastructure) | Limited or absent | Purpose-built (e.g., WebLOAD: concurrent user modeling, protocol-level load generation, SLA validation) |
| Cloud + On-Prem Support | Self-managed for both | Cloud-only (typically) | Both (critical for regulated industries) |
| CI/CD Integration | Plugin-dependent | Native for popular pipelines | Native + API-driven orchestration |
| Vendor Support | Community forums | Tiered support plans | Dedicated support, hands-on consulting |
RadView’s WebLOAD platform occupies a specific position in this landscape: purpose-built for performance and load testing with JavaScript-based scripting, AI-accelerated correlation for dynamic parameter handling, support for 100+ network protocols, and deployment flexibility across cloud and on-premises environments. For teams whose primary gap is performance validation at scale – the category most commonly underserved by open-source utilities and SaaS platforms – it provides the depth that general-purpose tools cannot match; for a detailed comparison of options in this category, see how to choose a performance testing tool.
Building a QA Strategy That Scales: From Reactive Firefighting to Proactive Quality
A QA strategy isn’t a document that lives in Confluence – it’s a set of operational practices, quality gates, and feedback loops that evolve with your team’s maturity. Here’s a four-stage progression:
- Ad-hoc – Testing happens when someone remembers. No documented test plans, no automation, no quality metrics. Defects found primarily by users.
- Managed – Test plans exist for major features. Some automation (mostly unit tests). Defect tracking is centralized. Release decisions still gut-feel.
- Measured – Quality gates block deployments when test pass rates drop below thresholds (e.g., < 95% pass rate on regression suite = blocked deploy). Performance baselines established. DORA metrics (deployment frequency, change failure rate, MTTR) tracked and reviewed [3].
- Optimized – Risk-based test prioritization allocates automation investment to highest-impact areas. AI-assisted anomaly detection flags regressions before human review. Continuous feedback from production monitoring feeds back into test case generation. Testing is fully integrated into CI/CD, not a separate phase.
Most teams are stuck between stages 1 and 2. Moving to stage 3 requires three concrete investments: automated quality gates in your pipeline, a regression suite with > 80% automation coverage on critical paths, and a performance testing practice that runs before every major release – not after the first outage.
Frequently Asked Questions
Is 100% test automation coverage worth the investment?
Not always – and chasing it often creates more problems than it solves. The maintenance cost of automated tests follows a diminishing-returns curve: automating the first 70% of deterministic, high-frequency tests typically captures 90%+ of the defect-prevention value. The remaining 30% often involves exploratory, UX-evaluation, and highly variable scenarios where manual testing delivers faster, more accurate results. Aim for strategic automation coverage, not completeness metrics.
How do I justify performance testing investment to leadership that hasn’t experienced an outage yet?
Use the NIST cost-multiplier data: defects found post-release cost up to 880x more to fix than those caught at the requirements stage [1]. Frame performance testing not as insurance against unlikely disasters, but as the validation step that determines whether your infrastructure investment is correctly sized. A single load test that reveals you need 3 application instances instead of 8 pays for the entire annual tooling cost.
Should my team adopt AI-assisted testing tools now, or wait for the technology to mature?
Adopt selectively now. Self-healing locators and intelligent correlation (for dynamic parameter handling in load tests) are production-proven and deliver measurable time savings today. AI-generated test cases and autonomous exploratory testing still require significant human review. Start with AI features that reduce toil on tasks your team already does manually – correlation, test data generation, flaky test diagnosis – rather than expecting AI to replace test design judgment.
What’s the minimum viable performance testing practice for a team that currently does none?
Start with three elements: (1) A baseline load test against your most critical user journey (e.g., login → search → checkout) at your expected peak concurrency. (2) A defined SLA threshold – e.g., p95 response time < 800ms, error rate < 0.5% under 5,000 concurrent sessions. (3) A CI/CD-triggered run before every major release. This three-element practice catches the majority of performance regressions without requiring a full-time performance engineering team.
How do I prevent my automation suite from becoming a maintenance burden that nobody wants to own?
Treat automation code with the same engineering discipline as production code: enforce code review on test scripts, apply design patterns (Page Object Model for UI, builder pattern for test data), assign explicit ownership of suite health in sprint rotations, and track automation ROI metrics (defects caught by automation vs. maintenance hours invested). If your maintenance-to-detection ratio exceeds 3:1 for any test category, that category needs architectural refactoring, not more tests.
–
Tool comparison section disclaimer: Tool features, pricing tiers, and capabilities referenced in this guide reflect information available at time of publication and are subject to change. Always verify current pricing and feature sets directly with vendors before making purchasing decisions. Performance testing results and cost-of-defect figures cited from NIST and DORA research are based on studies conducted at the dates referenced; actual results will vary based on application architecture, team size, and testing environment.
References and Authoritative Sources
- RTI for National Institute of Standards and Technology. (2002). Planning Report 02-3: The Economic Impacts of Inadequate Infrastructure for Software Testing. Prepared by RTI Health, Social, and Economics Research under Gregory Tassey, Ph.D., NIST. Retrieved from https://www.nist.gov/system/files/documents/director/planning/report02-3.pdf
- International Software Testing Qualifications Board (ISTQB®). (N.D.). What We Do – Certifications, Standards, and Testing Body of Knowledge. ISTQB®. Retrieved from https://www.istqb.org/what-we-do/
- Google Cloud DORA Research Program. (2025). Capabilities: Test Automation. DevOps Research and Assessment (DORA). Retrieved from https://dora.dev/capabilities/test-automation/